What is social engineering?
Social engineering is when a bad actor uses deception to manipulate a victim to give up confidential information, make a payment or share access to their online accounts. A scammer will often pose as a legitimate business to convince a customer to hand over information such as social security number or bank account details.
Organizations are not only at risk of their customers being targets, but their employees too, as scammers seek to extract confidential information, customer data or gain access to their business systems.
Types of social engineering attacks
Phishing (a collective term for most social engineering attacks) is when a fraudster (often via an SMS, email or phone call) convinces the victim to input information into a fake website or ask them to download a file that contains malicious software. The message is likely to be spoofed to look like it comes from a real contact or a known brand and is crafted so that the victim feels a sense of fear and / or urgency to comply.
The frequency of these messages globally is high – in the UAE for instance, people are more likely to receive an email from a fraudster than they are from a member of their family.
Spear phishing and whaling are types of phishing where the victim is a high-value target such as a CFO or a politician.
Vishing is the specific practice of making scam phone calls or leaving voicemails. Like phishing this may be used to gain information, but it is also a tactic used to convince a victim to make payment with the scammer often staying on the call to coach their victim through security blockers. This method of social engineering is commonly referred to as authorized push payment (APP) in the United Kingdom.
Smishing is similar to phishing, but the scammer uses text message to send out their requests which often ask for the victim to click on a link. Bad actors can spoof known brands and automate their attacks sending out a large numbers of messages.
The ease and frequency of smishing scam attempts has lead to only 5% of global consumers in 2021 thinking SMS is a safe way to communicate with a business.
Coupled with phishing, vishing or smishing, pretexting is the act of a scammer claiming to be someone in authority or someone the victim trusts. For a consumer this could be receiving a text from the IRS requesting payment, for an employee this may be a senior manager asking them to urgently download a file.
Baiting is the practice of using 'a too-good-to-be true offer' to convince the victim into transferring funds only to never receive the goods. This tactic is most typically deployed across social media and online adverts, however targeted SMS and emails are also used.
This method is also used to deploy malware onto users devices or harvest personal information. Online adverts or emails convince the victim to visit a spoofed landing page, leading then to mistakenly download a malware file or fill out personal details.
Social engineering by numbers
Online fraud is more than just a security concern, it’s your reputation that’s on the line. Download the report here.
Social engineering attack examples
A social engineering attack can consist of multiple stages, with a number of tactics used in order to achieve their goal. Some of the more common tactics are outlined below.
Layered protection against social engineering and scams
The first step is assessing for bad actors trying to hack or spoof a system to undermine its security, a common tactic of social engineering scams and remote access takeovers.
Our threat detection solutions check for known vulnerabilities against multiple malware engines, ensuring the session is secure. We also flag risks to an individual session such as if a device is jailbroken, tampered with, or using an emulator.
How threat detection reduces the effects of social engineeringOur bot detection technology checks whether there is a bot active in the session. We identify behaviors that indicate that a bot attack is underway and flag it if so, letting you to choose whether to end the session or to dynamically select the appropriate onward action within our Orchestration Layer.
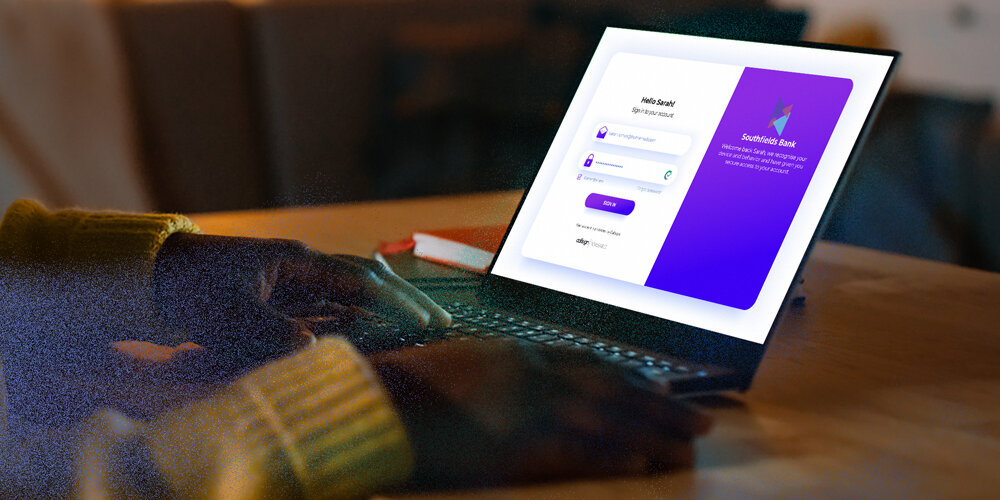
Prevent bot attacksWe analyze more data signals across web and mobile than any other vendor. Combining device, location, and threat intelligence with our unique Muscle Memory Technology – the highest fidelity form of behavioral biometrics – we more accurately identify the individual and ensure only the legitimate user has access to their accounts.
Reduce account takeover with Callsign's Intelligence EngineOur Orchestration Layer leaps into action when a customer exhibits unusual activity that indicates social engineering or an online scam is taking place. By inserting contextual questions into the customer journey, we provide a cognitive jolt to a user, giving organizations extra context to make risk-based decisions.
Callsign’s threat detection technology prevents remote access scams where a legitimate user’s session had been taken over by a RAT after login. Once this has been identified our system can step-up authentication or take another action in line with an organization’s policy.
As new capabilities go into production, new policies and regulations come into force, and bad actors develop increasingly devious ways to bypass security measures.
Callsign’s Orchestration Layer gives you the control to change adapt with your business – in real-time. With our low code/no code Orchestration Layer you can design, control, and deploy personalized user journeys that are both seamless and secure. With Callsign you can take a proactive stance on social engineering and scams.
Understand Callsign's Orchestration layerA digital solution for a digital problem
Callsign delivers industry-leading AI combining behavioral biometrics, location and device analysis to passively confirm user identity.