Welcome to our documentation portal
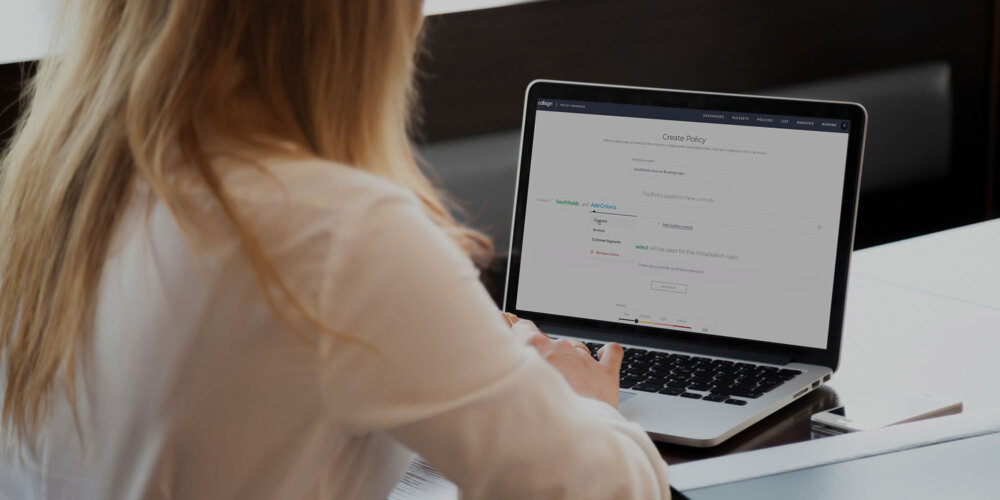
Discover the breadth and scope of the Callsign solution – whether that's designing simple and secure journeys, configuring policies or deploying new authenticators
Register for access
For access to our developer documentation you'll need to register your details. Just fill out the form and we'll be in touch.
Already signed up? Welcome back, you can click here to login
Looking for support?
Our dedicated team can help.